FIPS 140-2 is the de-facto standard to certify cryptography implemented in ICT products
What is FIPS 140?
FIPS 140 is a U.S. government standard that specifies the security requirements for cryptographic modules used to protect sensitive information. The standard ensures that encryption technologies—such as those used in software, hardware devices, and firmware—meet strict security criteria before they can be used by U.S. federal agencies or organizations working with government data.
FIPS 140 is published by the National Institute of Standards and Technology (NIST) and applies to products that perform cryptographic functions like encryption, decryption, digital signatures, and key generation.
What is the current version of FIPS 140?
FIPS 140-3 is the third and current version of the Federal Information Processing Standard governing the security requirements for cryptographic modules. It specifies how cryptographic hardware and software protecting sensitive data must be designed, implemented, and validated for federal use.
The standard matters because it establishes a widely recognized benchmark for cryptographic assurance, influencing both government procurement and global cybersecurity compliance frameworks.
Key facts
- Full name: Federal Information Processing Standard Publication 140-3
- Issued by: National Institute of Standards and Technology (NIST)
- Effective date: September 22, 2019
- Supersedes: FIPS 140-2 (2001)
- Basis: ISO/IEC 19790:2012 and ISO/IEC 24759:2017
Background and Scope of FIPS 140-3
FIPS 140-3 sets criteria for the design and testing of cryptographic modules—components providing encryption, decryption, digital signatures, and key management. It applies to modules used in federal information systems that handle sensitive but unclassified data. Non-federal organizations often adopt it voluntarily for compatibility or to meet industry regulations.
Major changes from FIPS 140-2
The update aligns the U.S. standard with international cryptographic standards (ISO/IEC 19790 and 24759). It refines the four security levels, enhances physical and logical protection requirements, and introduces concepts such as non-invasive attack mitigation. Testing and validation now follow international procedures coordinated by the Cryptographic Module Validation Program, jointly managed by NIST and the Communications Security Establishment.
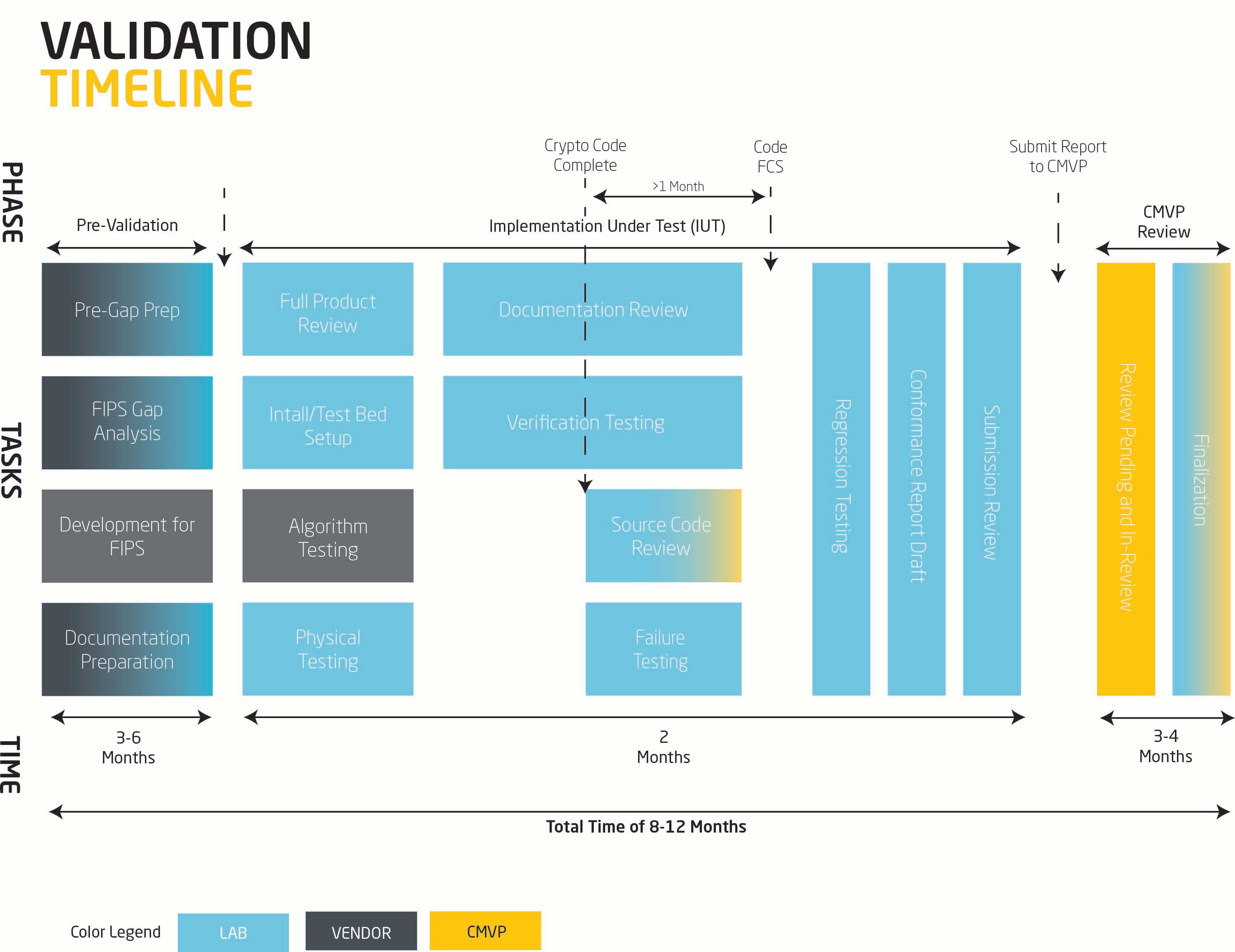
Validation process and Ongoing relevance
To achieve FIPS 140-3 compliance, vendors submit their modules to accredited Cryptographic and Security Testing (CST) Laboratories. These labs perform standardized tests covering areas such as roles, services, physical security, key management, and self-tests. Successful modules receive a validation certificate published on the NIST CMVP website.
FIPS 140-3 underpins trust in U.S. government encryption systems and influences commercial security certifications worldwide. Its alignment with ISO standards facilitates mutual recognition, supporting global interoperability in cryptographic assurance.
FIPS 140 Security Levels
FIPS 140 defines four increasing levels of security assurance:
| Security Level | Description |
| Level 1 | Basic security requirements using approved cryptographic algorithms and production-grade components. |
| Level 2 | Adds tamper-evidence and role-based authentication to help detect unauthorized access. |
| Level 3 | Requires tamper-resistant hardware, stronger identity-based authentication, and separation of critical security parameters. |
| Level 4 | The highest level, providing robust physical security and environmental protection, designed to detect and respond to physical attacks. |
Intertek FIPS 140 Solutions
We seek to engage early on and adopt risk mitigating processes whereby non-compliance is identified early on, fixes are discussed and planned, testing methodology is defined in advance to allow your teams to plan accordingly and schedule is tracked religiously to ensure our progress is in step with your development and test plans.
We have leveraged our considerable experience in FIPS 140 validation to develop custom tools and processes to offer a best-of-breed certification experience to our clients.
FIPS 140-3 Validation
For vendors, a successful FIPS 140-3 validation can be essential to selling their products in US and international markets:
- In the U.S., the DoD and NIAP NSTISSP No. 11 require FIPS 140 validation for cryptographic modules used by federal government agencies to store, transmit or protect sensitive, but unclassified information (see section 3.2 of the FIPS 140-3 FAQ for details).
- In Canada, the CSEC recommends federal agencies use FIPS 140 validated cryptographic modules to secure data designated as Protected A or Protected B.
- In the U.K., the Communications-Electronics Security Group (CESG) recommends the use of FIPS 140 validated cryptographic modules.
FIPS 140 Algorithm Testing
Algorithm testing is an important step for the FIPS module validation process. While it is the most objective part of the validation process, it does not require specialized tools or skills to execute.
FIPS 140 Service Offerings:

Knowledge Center
- Cybersecurity Awareness Training Fact Sheet
- Common Criteria Certification Process Fact Sheet
- FIPS 140-3 Process and Service Offerings Fact Sheet
- Cyber Security Risk in a Mass Remote Working Environment Webinar
- Intertek Cyber Assured Fact Sheet
- Consumer Product Focused Cyber Security Test and Certification Program
- PCI PIN Transaction Security (PTS) Cyber Security Fact Sheet
- Cyber Security Assurance Overview
- ANSI/UL 2900 Cyber Security Assessments Fact Sheet

Upcoming Events
Cybersecurity Assurance Overview
Intertek provides tailor-made security solutions designed and executed based upon risk factors commonly associated with your specific product and industry.